Privacy & Security
Waypoint's system architecture prioritizes user privacy while maintaining accurate recreation activity monitoring capabilities.
Privacy-Preserving Architecture
The Waypoint system is designed from the ground up to preserve user privacy while collecting accurate recreation activity data.
No Facial Recognition
Waypoint's detection models identify activity types (hikers, bikers, etc.) without facial recognition or individual identification capabilities. The system cannot identify specific individuals.
Privacy Blur Applied Automatically
All images are processed through an AI privacy blur filter that obscures faces and identifying features. No original, unblurred photos are stored on the cloud—only the privacy-filtered versions are retained.
Automatic Image Deletion
Privacy-blurred images are automatically deleted after 30 days. Only aggregate count data and anonymized detection metadata are retained long-term.
Aggregate Data Only
Publicly shared data consists of aggregate counts and statistics. Individual detection events are not exposed outside secure processing systems.
Data Handling & Retention
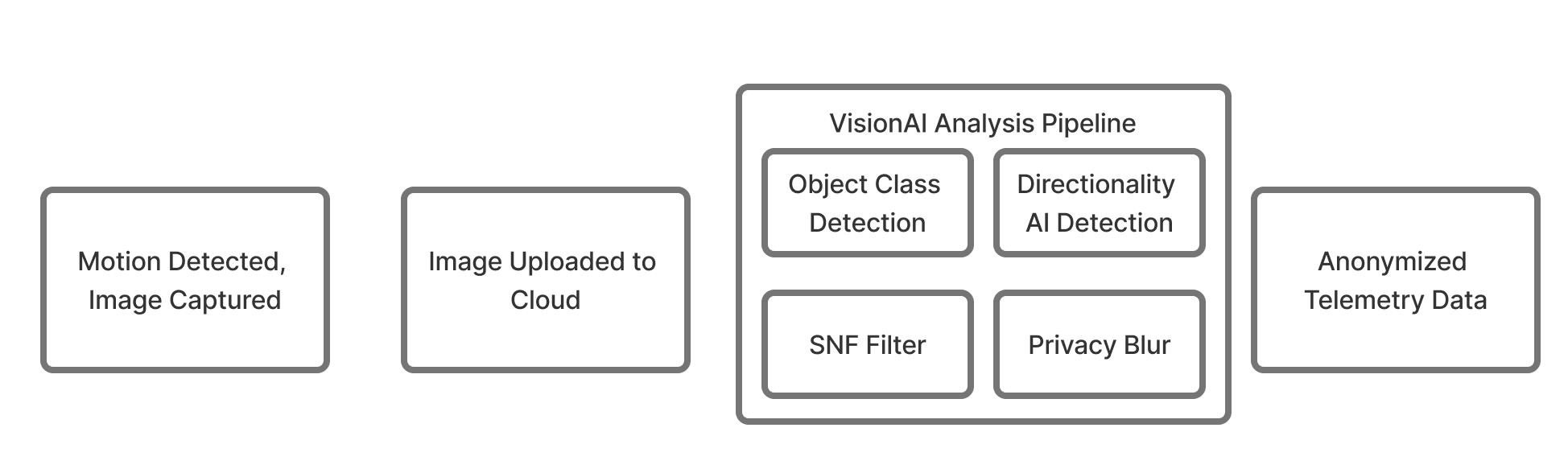
Privacy-First Processing Pipeline
When motion is detected, images are captured and uploaded to the cloud for AI analysis. The VisionAI pipeline applies privacy-preserving techniques as the final processing step—ensuring no original photos are ever stored.
Data Retention Policy
Example Privacy-Blurred Images
These are examples of the privacy-filtered images stored on the cloud. All faces and identifying features are automatically obscured. These images are retained for 30 days for quality assurance and model validation, then permanently deleted.


System Security
Data Encryption
- •End-to-end encryption for cellular transmission
- •TLS 1.3 for data in transit
- •AES-256 encryption at rest
- •Encrypted storage on camera hardware
Access Control
- •Role-based access control (RBAC)
- •Multi-factor authentication (MFA)
- •Audit logging for all data access
- •Granular permission management
Network Security
- •VPN connectivity for camera networks
- •Firewall protection
- •Intrusion detection systems
- •Regular security audits
Physical Security
- •Lockable camera enclosures
- •Tamper detection alerts
- •Secure mounting hardware
- •Anti-theft cable systems
Privacy Compliance & Transparency
Public Space Monitoring
Waypoint cameras are deployed in public outdoor spaces where individuals have no reasonable expectation of privacy, similar to traditional trail counters and traffic monitoring systems.
Transparent Deployment with Public Information Tags
All Waypoint cameras are equipped with visible public information tags that clearly identify the camera's purpose, contact information, and privacy policies. These tags ensure complete transparency about data collection activities.

Partner Data Agreements
Deployments are conducted in partnership with land managers under formal data sharing agreements that specify data usage, retention, and access policies.
Privacy Comparison
| Feature | Waypoint | Traditional Security Cameras |
|---|---|---|
| Facial Recognition | No | Often Yes |
| Privacy Blur Filter | Yes (Automatic) | No |
| Original Image Storage | Never Stored | Yes (Often Indefinite) |
| Individual Identification | No | Possible |
| Auto Image Deletion | Yes (30 days) | Rarely |
| Data Purpose | Aggregate Statistics | Security/Surveillance |